Cloud compliance standards create trust frameworks enabling enterprises to process sensitive data confidently across public cloud providers. GDPR, ISO 27001, and SOC 2 represent cornerstone regulations and certifications shaping cloud security practices globally, protecting customer information while satisfying regulatory authorities. Digital marketers handling campaign databases or BBA students building compliant cloud architectures need a comprehensive understanding to ensure business continuity and legal protection.
GDPR Establishes Data Protection Foundation
The General Data Protection Regulation governs EU citizens' personal data processing, imposing strict accountability requirements across cloud environments worldwide. Cloud compliance standards begin with GDPR Article 32 mandating appropriate technical organizational measures protecting data confidentiality, integrity and availability against unauthorized access, loss or destruction. Data Protection Impact Assessments become mandatory when processing high-risk datasets requiring formal risk treatment plans demonstrating compliance throughout the cloud lifecycle.
Territorial Scope Creates Global Obligations
GDPR cloud compliance extends beyond EU borders, applying to any organization processing EU resident data, regardless of location, establishing extraterritorial jurisdiction. Cloud service providers must offer GDPR-compliant data residency options enabling customers to maintain control over geographic data location, satisfying localization requirements. Data Processing Agreements between controllers and processors formalize responsibilities, clearly defining security obligations, audit rights and breach notification timelines.
Data Subject Rights Drive Architecture Decisions
Cloud compliance standards incorporate GDPR data subject rights, including access, rectification, erasure and data portability, creating operational imperatives for cloud architectures. Right to Erasure demands verifiable data deletion across distributed cloud storage systems, including backups, snapshots and replicas, proving destruction. Automated data subject request workflows integrate directly with cloud IAM systems, enabling rapid fulfillment without compromising legitimate business processing.
ISO 27001 Provides Information Security Framework
International Organization for Standardization 27001 establishes a systematic approach to managing information security risks through a globally recognized certification process. Cloud compliance standards leverage ISO 27001 Annex A controls, providing comprehensive coverage across organizational technical controls, including access control, cryptography and operations security. Statement of Applicability documents control implementation status, creating auditable evidence demonstrating risk-based security decision-making throughout cloud operations.
Risk Assessment Drives Continuous Improvement
ISO 27001 cloud compliance requires a formal risk assessment methodology, identifying threats, vulnerabilities, calculating business impact and establishing treatment priorities. Risk treatment plans specify control implementation timelines, responsibilities, acceptance criteria, creating an actionable roadmap, achieving certification and maintaining compliance. Internal audits validate control effectiveness across cloud environments, identifying gaps requiring remediation before external certification audits occur.
Management Review Ensures Strategic Alignment
Cloud compliance standards incorporate the ISO 27001 management review process, ensuring executive commitment translates into resource allocation policy enforcement across cloud operations. Key performance indicators track control effectiveness, incident metrics compliance status feeding continuous improvement cycles mandated by the standard. Certification maintenance demands annual surveillance audits, recertification every three years and validating sustained security maturity enterprise-wide.
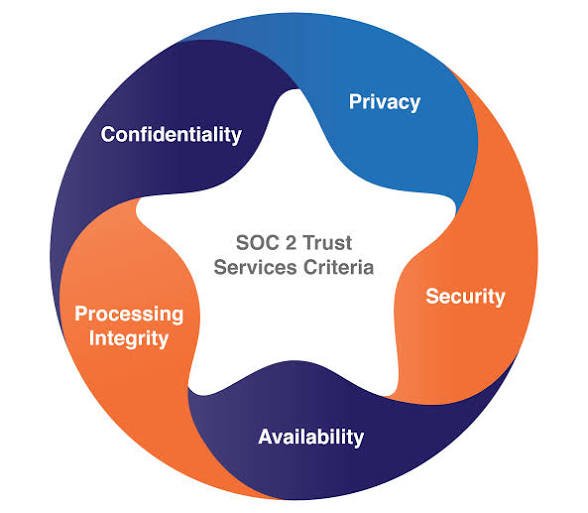
SOC 2 Defines Trust Service Criteria
System and Organization Controls 2 framework evaluates cloud service providers across five trust service criteria: security, availability, processing integrity, confidentiality and privacy. Cloud compliance standards utilize SOC 2 Type II reports, providing a detailed independent assessment of control effectiveness over a specified observation period, typically six to twelve months. Bridge letters extend report validity between issuance dates, maintaining continuous assurance for enterprise customers.
Security Trust Service Criterion Forms Foundation
SOC 2 cloud compliance begins with the security criterion encompassing logical and physical access controls, monitoring, incident response, change management and risk mitigation across cloud infrastructure. Common Criteria establishes baseline security requirements customized through additional criteria selection based on the service offering risk profile. Control Matrix maps requirements, specific controls implementation evidence, enabling auditors to validate design and operating effectiveness throughout the examination period.
Complementary Criteria Address Specific Risks
Availability criterion validates cloud infrastructure resilience, business continuity and disaster recovery capabilities, ensuring service uptime meets contractual obligations. Processing Integrity evaluates data processing accuracy, completeness, authorization and maintenance across cloud workflows. Confidentiality Privacy criteria protect sensitive regulated data throughout the lifecycle, preventing unauthorized disclosure across multi-tenant cloud environments.
Shared Assessments Streamline Compliance
Cloud compliance standards leverage Shared Assessments SIG questionnaires, establishing standardized control validation across industry participants, reducing redundant audit efforts. Continuous Monitoring questionnaires assess real-time control monitoring capabilities, distinguishing mature organizations relying on periodic assessments. Enterprise customers utilize standardized assessment materials, minimizing vendor onboarding timelines and accelerating cloud adoption confidently.
Integrated Compliance Management Platform
Modern cloud compliance standards demand integrated governance risk management platforms unifying GDPR, ISO and SOC2 requirements across multi-cloud environments. Policy management centralizes control, documentation, version control and distribution tracking across global teams, ensuring consistent implementation. Continuous control monitoring automates evidence collection, validating control operation across the distributed cloud infrastructure, eliminating manual audit preparation efforts significantly.
Data Residency Localization Requirements
GDPR cloud compliance mandates explicit data residency decisions, preventing unintended cross-border transfers violating localization requirements. ISO 27001 controls address geographic data location through formal risk assessment, documenting business legal implications in specific jurisdictions. SOC 2 reports detail data storage transmission locations, enabling customers to validate compliance with geographic regulatory requirements systematically.
Vendor Management Extends Compliance Boundary
Cloud compliance standards require third-party risk management to evaluate cloud service provider subcontractors across the entire supply chain comprehensively. Right-to-audit clauses enable validation of vendor security claims, independent assessment, control implementation and evidence collection. Vendor risk scoring quantifies third-party exposure, prioritizing remediation efforts across the cloud ecosystem strategically.
Employee Training Certification Requirements
GDPR Article 39 mandates a Data Protection Officer for organizations processing significant personal data volumes regularly. ISO 27001 requires security awareness training certification programs to ensure personnel competency across cloud operations consistently. SOC 2 validates training program effectiveness through independent audit evidence demonstrating behavior change reduced security incidents across the organization.
Automated Compliance Evidence Collection
Cloud compliance standards embrace policy-as-code infrastructure-as-code approaches, generating auditable evidence automatically throughout the deployment lifecycle. Continuous compliance platforms validate configuration policies and infrastructure code, preventing non-compliant resources from reaching production environments proactively. Audit-ready reporting generates executive dashboards, compliance status, risk exposure and regulatory requirements instantly across business units.
Start Compliance Journey Strategically
Begin cloud compliance standards implementation, prioritizing GDPR data encryption, MFA, public access blocking, immediate priorities and establishing a security foundation. Layer ISO 27001 risk management, SOC 2 trust criteria, incrementally building a comprehensive compliance framework supporting digital transformation confidently. Consistent execution transforms regulatory burden strategic advantage, enhancing enterprise competitiveness, customer confidence and market differentiation.