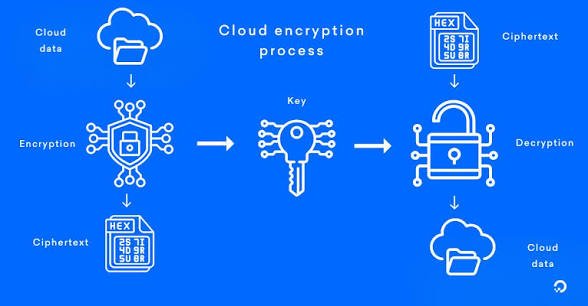
Cloud encryption converts readable data into unreadable ciphertext using algorithms and keys, ensuring only authorized parties can access it. It protects sensitive information stored or transmitted in cloud platforms like AWS, Azure, or Google Cloud against breaches and leaks. This process is vital as cloud adoption grows, with encryption acting as a core defense layer alongside access controls.
Without encryption, data at rest on servers or in transit over networks becomes vulnerable to interception or theft. Modern clouds offer built-in tools, but proper implementation prevents most ransomware and insider threats.
Types of Cloud Encryption
Cloud encryption falls into symmetric and asymmetric categories, each suited for specific scenarios.
- Symmetric Encryption: Uses one shared key for both encrypting and decrypting; fast for large datasets with algorithms like AES-256.
- Asymmetric Encryption: Employs public-private key pairs (e.g., RSA, ECC); ideal for secure key exchanges but slower for bulk data.
Encryption Methods in the Cloud
Data at Rest Encryption: Secures stored files using server-side (SSE) managed by providers or client-side (CSE) done before upload.
Data in Transit Encryption: Protects moving data via TLS/SSL protocols, creating secure tunnels for uploads/downloads.
End-to-End Encryption (E2EE): Ensures data remains encrypted from sender to receiver, with no intermediary access, common in collaboration tools. Key management services (KMS) like AWS KMS handle rotation and storage securely across these methods.
Benefits of Cloud Encryption
Encryption ensures data confidentiality, integrity, and compliance with regs like GDPR, HIPAA, and PCI-DSS by rendering stolen data useless. It reduces breach impacts, as encrypted data cannot be exploited even if accessed.
Businesses gain trust from customers, avoid fines, and enable secure multi-tenant clouds. Advanced methods like homomorphic encryption allow analytics without decryption risks.
Best Practices for Implementation
Classify and Prioritize Data: Assess sensitivity first, encrypting high-value assets like PII or financials.
Use Provider Tools with KMS: Leverage managed services for automatic key rotation; avoid hardcoding keys.
Combine SSE and CSE: Apply SSE for convenience, CSE for max control on ultra-sensitive data.
Enforce TLS 1.3 Everywhere: Mandate strong protocols for transit; monitor with tools like CASB.
Regular Audits and Rotation: Review access logs, rotate keys quarterly, and test decryption recovery.
Common Challenges and Solutions
Key mismanagement exposes risks solution: centralized KMS with HSMs for hardware protection. Performance overhead from encryption? Opt for hardware-accelerated AES on modern clouds.
Multi-cloud setups complicate uniformity; standardize via policy-as-code tools like Terraform. Legacy app integration? Use proxies or gateways for transparent encryption.
Future Trends in Cloud Encryption
Quantum threats loom, pushing post-quantum cryptography like lattice-based algorithms into standards. AI-driven key management and zero-knowledge proofs will enhance privacy. By 2026, expect homomorphic encryption to be mainstream for compliant AI workloads in regulated sectors.