In 2026, as enterprises manage sprawling multi-cloud environments across AWS, Azure, and GCP, fragmented security practices lead to breaches costing millions. A cloud security governance framework provides the structured approach needed to embed security into every cloud decision, balancing innovation speed with risk control. This detailed guide outlines proven components, implementation steps, and tools to create enterprise-grade cloud security governance.
What is Cloud Security Governance?
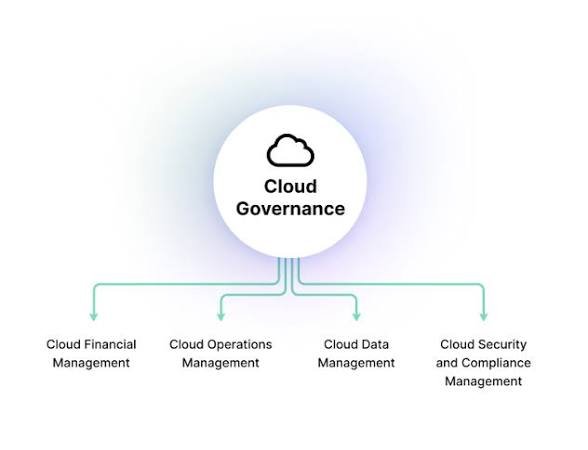
Cloud security governance establishes policies, processes, roles, and controls, ensuring cloud environments meet security, compliance, and business objectives. Unlike traditional IT security focused on hardware perimeters, cloud governance addresses dynamic shared responsibility models where customers own data, access, and configurations while providers secure the underlying infrastructure.
Effective frameworks align technical controls with organizational risk tolerance, regulatory mandates (GDPR, HIPAA, SOC 2), and business priorities. They transform security from a cost center into a strategic enabler, preventing shadow IT while accelerating secure cloud adoption across dev, sec, and ops teams.
Core Pillars of Enterprise Cloud Security Governance
Successful frameworks rest on six interdependent pillars, each addressing specific governance challenges in distributed cloud architectures.
1. Policy Management and Standards
Define clear, actionable cloud security policies covering data classification, encryption standards, access controls, configuration baselines, and change approval processes. Translate enterprise security standards into cloud-specific requirements: S3 bucket policies, IAM least privilege rules, Kubernetes RBAC standards.
Policy-as-code (OPA, Sentinel, CloudFormation Guard) embeds rules into CI/CD pipelines, preventing non-compliant deployments. Version policies like code; conduct annual reviews against new threats and regulations.
2. Risk Management Framework
Implement continuous risk assessment, identifying cloud-specific threats: IAM over-privileging, public storage buckets, unpatched workloads, supply chain vulnerabilities in containers. Risk scoring combines likelihood, impact, and exploitability; prioritize using quantitative models (CVSS + business context). Quarterly risk workshops align security investments with executive risk appetite.
3. Identity and Access Governance
Cloud IAM complexity demands continuous entitlement management. Map every principal (users, services, workloads) to business-justified permissions using CIEM (Cloud Infrastructure Entitlement Management) tools. Implement just-in-time, just-enough access via temporary credentials and session monitoring.
Zero Standing Access eliminates long-lived credentials; workload identity federation prevents secret sprawl. Quarterly access reviews, break-the-glass procedures, and anomaly-based deprovisioning maintain hygiene.
4. Compliance Management and Reporting
Automate evidence collection for SOC 2, ISO 27001, PCI-DSS using cloud-native compliance operators (AWS Audit Manager, Azure Policy Insights). Continuous control monitoring generates audit-ready reports; exception management tracks risk-accepted deviations with expiration dates.
Governance Operating Model and RACI
A clear organizational structure prevents the diffusion of responsibility. Establish Cloud Center of Excellence (CCoE) owning framework design, tooling, and policy enforcement. RACI matrices define:
Cloud Security Board (Accountable): Executive oversight, risk acceptance
Cloud Security Architect (Responsible): Framework design, control implementation
Cloud Operations (Responsible): Daily operations, incident response
Application Teams (Consulted): Secure development practices
Internal Audit (Informed): Independent validation
Implementation Roadmap: 90-Day Sprint Cycles
Phase 1: Assess and Plan (Days 1-30)
Inventory all cloud accounts, workloads and data flows. Baseline current security posture using CSPM tools (Prisma Cloud, Wiz). Gap analysis against CIS Benchmarks, NIST CSF. Define risk-based implementation priorities.
Phase 2: Policy and Control Deployment (Days 31-60)
Roll out policy-as-code, IAM baselines, encryption defaults via cloud-native tooling (AWS Organizations, Azure Policy, GCP Organization Policies). Deploy CSPM for continuous monitoring; integrate with Slack/PagerDuty.
Phase 3: Automation and Guardrails (Days 61-90)
Implement CI/CD security gates (Checkov, Terrascan), service control policies (SCPs), and tagging enforcement. Launch monthly compliance dashboards tracking control effectiveness.
Essential Tools and Technology Stack
Cloud-Native Governance:
- AWS Organizations + SCPs: Account baselines, guardrails
- Azure Policy + Blueprints: Compliance-as-code
- GCP Organization Policies: Centralized constraints
Third-Party Platforms:
- CloudQuery/Wiz: Multi-cloud posture management
- OPA Gatekeeper: Policy enforcement at runtime
- HashiCorp Sentinel/Terraform Cloud: IaC policy validation
Identity Governance:
- Silverfort/PAM: Zero Standing Access
- Saviynt/Cube: Cloud IAM analytics
Control Frameworks and Maturity Model
Adopt recognized standards providing structured control sets:
CIS Cloud Benchmarks: Configuration hardening (Level 1 within 90 days)
NIST CSF: Identify → Protect → Detect → Respond → Recover
CSA Cloud Controls Matrix (CCM): 197 controls across 17 domains
Maturity Levels:
- Initial: Ad-hoc security, reactive fixes
- Managed: Documented policies, basic monitoring
- Defined: Policy-as-code, automated compliance
- Quantitative: Risk-based prioritization, metrics-driven
Continuous Monitoring and Assurance
Implement control effectiveness scoring across five dimensions:
- Configuration Drift: CloudQuery/Terraform validate live vs. intended states
- Access Violations: IAM analytics, anomalous behavior detection
- Vulnerability Posture: Container/VM scanning integration
- Compliance Coverage: Automated evidence collection
- Threat Detection: Cloud-native SIEM (GuardDuty, Defender)
Weekly executive dashboards track progress against targets. Monthly control self-assessments by control owners—quarterly third-party validations.
Change Management and Exception Handling
Formal change advisory board reviews high-risk cloud changes. Exception requests document business justification, compensating controls, expiration dates, and the risk owner's signature. Automated workflows (ServiceNow, Jira) prevent policy bypasses.
Training and Cultural Adoption
Mandatory cloud security training: shared responsibility model, secure coding and incident reporting. Gamified capture-the-flag exercises build muscle memory. Embed security champions in dev teams; monthly lunch-n-learns showcase recent findings.
Metrics That Matter to Executives
Boardroom KPIs:
- Mean time to remediate (MTTR) critical issues
- Percentage of workloads with required controls
- Compliance coverage across audit frameworks
- Cloud security incidents prevented vs. total possible
- Cost of security controls vs. breach avoidance value
A mature cloud security governance framework transforms compliance burden into a competitive advantage. Enterprises mastering governance don't just avoid breaches; they enable faster innovation within secure boundaries, turning cloud complexity into strategic strength.