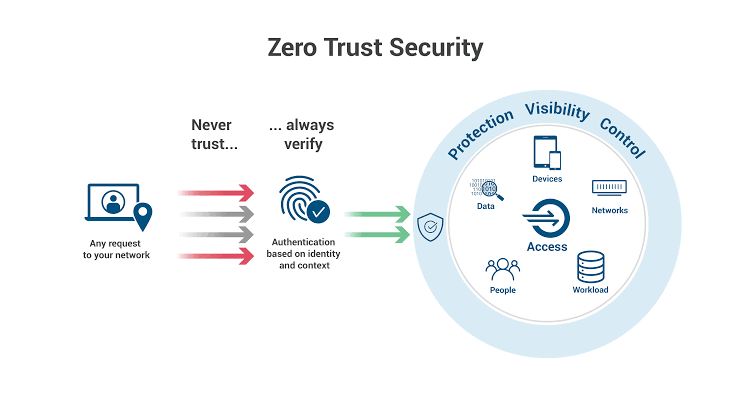
Zero Trust Architecture in Cloud shifts security from perimeter-based defenses to a model where no user, device, or application is trusted by default, regardless of location. Every access request undergoes continuous verification based on identity, context, and risk signals. This approach is essential in cloud environments where traditional firewalls fail against lateral movement by attackers.
Cloud adoption has exploded, but so have breaches exploiting misconfigurations and insider threats. Zero Trust ensures least privilege access, micro-segmentation, and real-time monitoring to minimize risks. Originating from Forrester's John Kindervag in 2010, it's now a standard for AWS, Azure, and Google Cloud.
Core Principles of Zero Trust
Zero Trust rests on "never trust, always verify," eliminating implicit trust zones. Key principles include explicit verification of all users, devices, and workloads; least privilege access to reduce exposure; and assuming breach for continuous monitoring.
In cloud contexts, this means contextual policies factoring in user role, device health, location, time, and behavior. Automation enforces these dynamically, adapting to threats without human intervention. For instance, a service account accessing sensitive data must re-prove its legitimacy per transaction.
Why Implement Zero Trust in Cloud Environments
Cloud's dynamic nature, multi-tenant setups, serverless functions, and hybrid workloads amplify risks like data exfiltration and zero-day exploits. Zero Trust counters these by containing breaches through segmentation, preventing attackers from pivoting.
Organizations report up to 50% faster threat detection and response post-implementation. Compliance with standards like NIST 800-207 or GDPR becomes simpler with auditable access logs. As hybrid/multi-cloud grows, Zero Trust unifies security across providers.
Step-by-Step Implementation Guide
Implementing Zero Trust Architecture in the cloud requires a phased approach: assess, design, deploy, and optimize. Start small with high-value assets before scaling.
Step 1: Assess Current Environment
Map your attack surface by inventorying assets, data, apps, users and devices. Use cloud-native tools like AWS Config or Azure Resource Graph for discovery. Identify vulnerabilities via audits, prioritizing critical "protect surfaces" like databases.
Conduct gap analysis against Zero Trust pillars. Tools like Wiz or Cloud Security Posture Management (CSPM) reveal shadow IT and over-permissions. Document baselines for identity, network, and endpoints.
Step 2: Define Protect Surface and Policies
Focus on crown jewels: sensitive data and crown jewel applications. Classify assets by risk using tags or labels in cloud consoles. Establish policies for least privilege, e.g., role-based access control (RBAC).
Align with frameworks like Google Cloud's Well-Architected. Policies should be dynamic, incorporating signals like anomaly detection.
Step 3: Strengthen Identity and Access Management (IAM)
Deploy multi-factor authentication (MFA), preferably phishing-resistant, like hardware keys. Centralize identities with providers like Okta, Azure AD, or AWS IAM Identity Center. Extend to machine identities service principals, Kubernetes pods with short-lived credentials.
Implement just-in-time (JIT) access and privileged access management (PAM). Enforce contextual auth: block logins from risky IPs or unhealthy devices.
Step 4: Apply Least Privilege and Micro-Segmentation
Audit permissions and revoke excesses using tools like AWS IAM Access Analyzer. Segment networks into zones with cloud-native features: AWS VPCs, Azure Virtual Networks, or Google VPC Service Controls.
Micro-segment workloadse.g., Istio service mesh for containers or AWS VPC Lattice. Limit east-west traffic to essential paths only.
Step 5: Secure Devices and Endpoints
Integrate endpoint detection and response (EDR) like CrowdStrike or Microsoft Defender. Require device compliance: encryption, patches, certificates via Intune or Jamf.
In the cloud, verify workload posture before access using agentless scanning.
Step 6: Enable Continuous Monitoring and Analytics
Deploy SIEM like Splunk or cloud-native logging (CloudWatch, Azure Sentinel). Monitor for anomalies with UEBA (user/entity behavior analytics)—Automate responses via SOAR tools.
Assume breach: run red-team simulations quarterly. Use AI-driven threat hunting for encrypted traffic visibility.
Step 7: Automate and Orchestrate
Leverage Infrastructure as Code (IaC) for policy enforcement, Terraform with OPA (Open Policy Agent). Automate provisioning/deprovisioning to avoid drifts.
Integrate CI/CD pipelines with security gates for shift-left protection.
Cloud Provider-Specific Best Practices
AWS Implementation
Use AWS Verified Access for app-level Zero Trust. Combine GuardDuty for threat detection, Nitro Enclaves for confidential computing, and Network Firewall for segmentation.
Azure Implementation
Leverage Azure AD for identity, Defender for Cloud for posture management, and Private Link for secure connectivity. Enforce conditional access policies.
Google Cloud Implementation
Apply BeyondCorp principles with Context-Aware Access. Use VPC Service Controls and Security Command Center for perimeter-less security.
Tools and Technologies for Zero Trust
Essential stack includes IAM (Okta, Ping), segmentation (Illumio, Cato Networks), monitoring (Datadog, Elastic), and orchestration (Palo Alto Prisma Cloud). Open-source options like SPIFFE for workloads or Falco for runtime security suit budgets.
Vendor-neutral: Zscaler or Netskope for SASE integration. Evaluate via PoCs, focusing on integration ease.
Common Challenges and Solutions
Challenge: Legacy app compatibility. Solution: Proxy with API gateways like Kong, gradually modernizing.
Challenge: User friction. Solution: JIT/PAM reduces routine MFA prompts. Train teams on value.
Challenge: Visibility gaps. Solution: Deep packet inspection or eBPF-based tools like Cilium.
Measuring Success and Continuous Improvement
Track metrics: mean time to detect/respond (MTTD/MTTR), permission sprawl reduction, breach containment rate. Conduct maturity assessments annually using NIST or CISA playbooks.
Iterate with automation roadmaps and cross-team governance. Zero Trust is evolutionary, measure, expand.