Identity and Access Management (IAM) serves as the gatekeeper in cloud environments, authenticating users and authorizing access based on roles and permissions. It ensures only verified identities reach resources, acting as the new perimeter in cloud-native setups where traditional firewalls fall short. In practice, IAM handles everything from user logins to machine identities like APIs, using policies to grant minimal necessary access.
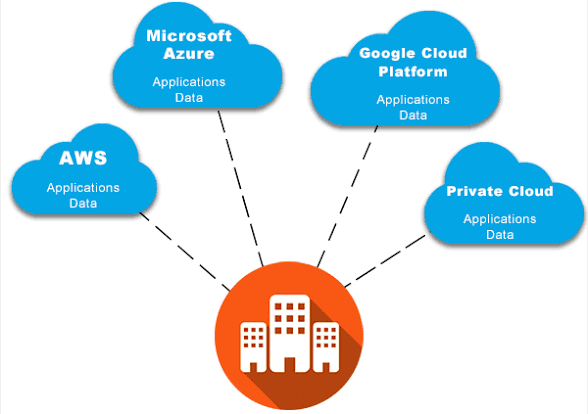
This framework integrates authentication (verifying "who you are") with authorization (defining "what you can do"), making it essential for multi-cloud setups across AWS, Azure, or Google Cloud. Without strong IAM, cloud assets like databases and storage become easy targets for credential theft.
Why IAM Matters for Cloud Protection
Cloud adoption has exploded, but so have risks over 80% of breaches involve compromised identities, highlighting IAM's role in stopping unauthorized entry. It provides centralized visibility, letting teams monitor access across providers and detect anomalies like privilege creep, where users gain excessive rights over time.
IAM also supports compliance with standards like GDPR and HIPAA by logging activities and enforcing granular controls. Businesses using IAM reduce breach costs significantly through proactive identity governance.
Core Components of Cloud IAM
- Authentication: Verifies identities via passwords, biometrics, or tokens; multi-factor authentication (MFA) adds layers to block 99% of account takeover attempts.
- Authorization: Uses role-based access control (RBAC) or attribute-based access control (ABAC) to assign least privilege, ensuring developers access only dev environments.
- Single Sign-On (SSO): Allows one login for multiple apps, cutting password fatigue while maintaining security.
- Federated Identity: Links external providers for seamless access without redundant credentials.
These elements work together to secure human and non-human identities, like service accounts.
Key Benefits of Implementing IAM
IAM streamlines operations by centralizing management, reducing admin overhead with automated provisioning and deprovisioning. It prevents shadow IT by tracking all access requests and enforces zero trust, verifying every action regardless of location.
Organizations gain granular privilege control, cutting insider threats and lateral movement by attackers. Plus, regular audits via IAM logs help maintain compliance and quick incident response. Overall, it boosts efficiency while slashing risks in dynamic cloud landscapes.
IAM Best Practices for Robust Security
Enable Multi-Factor Authentication (MFA): Mandate it everywhere to thwart stolen credentials; combine with password rotation every 90 days.
Adopt Zero Trust and Least Privilege: Grant just-in-time (JIT) access based on context like device or location, using RBAC/ABAC to avoid over-permissioning.
Centralize Identity Management: Use native tools like AWS IAM or Azure AD for unified policies across multi-cloud setups; integrate with enterprise directories.
Audit and Monitor Regularly: Review logs for suspicious activity, rotate secrets for machines, and classify assets by sensitivity before assigning roles.
Secure Privileged Accounts with PAM: Isolate high-risk admin access and watch for shadow IT with CASB tools.
Common IAM Challenges and Solutions
Rapid cloud scaling leads to privilege creep and unmanaged machine identities, solved by automated audits and behavioral monitoring. Multi-cloud complexity? Federated systems unify controls without silos.
Integration hurdles with legacy systems improve via SSO and CIAM, ensuring customer and employee identities align securely. Poor visibility into Shadow IT? Regular asset inventories and DLP policies close gaps.
Future of IAM in Cloud Security
As zero trust evolves, IAM will incorporate AI for anomaly detection and dynamic policies, handling rising machine-to-machine interactions. Expect tighter integration with SASE for holistic protection. By prioritizing IAM now, businesses future-proof against evolving threats in 2026's cloud-first world.