As cloud environments become more complex and distributed, traditional security approaches are no longer sufficient. The rise of remote work, multi-cloud strategies, and sophisticated cyber threats has led to the adoption of a more advanced approach known as the Zero Trust security model.
Zero Trust is a modern security framework that assumes no user, device, or system should be trusted by default, whether inside or outside the network. Every access request must be verified before granting permission.
What Is the Zero Trust Security Model
The Zero Trust security model is based on the principle of “never trust, always verify.” Unlike traditional perimeter-based security, which assumes that everything inside the network is safe, Zero Trust treats every access attempt as potentially malicious.
In cloud computing, this model is particularly important because users and applications can access resources from anywhere, making traditional boundaries irrelevant.
Zero Trust ensures that access is granted only after strict identity verification, device validation, and security checks.
Why Zero Trust Is Important in Cloud Computing
Cloud environments are highly dynamic, with users accessing resources from multiple locations and devices. This increases the risk of unauthorized access and data breaches.
Zero Trust minimizes these risks by continuously verifying identities and enforcing strict access controls. It helps organizations secure their cloud infrastructure even in highly distributed environments.
It also aligns well with modern security needs, where threats can originate both inside and outside the network.
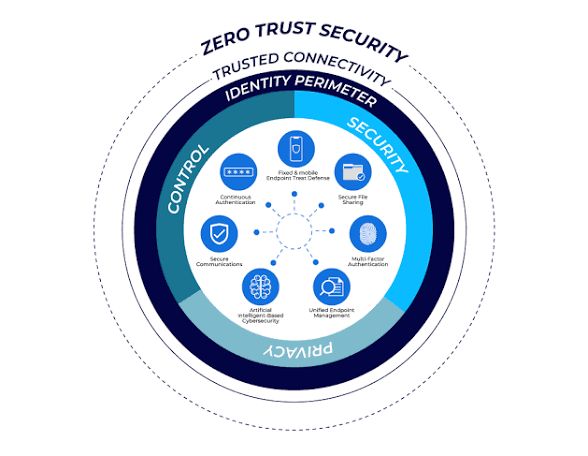
Core Principles of Zero Trust
Zero Trust is built on several key principles that define how it operates.
Verify Explicitly means every user and device must be authenticated and authorized before accessing resources. This includes using multi-factor authentication and analyzing user behavior.
Least Privilege Access ensures that users only get access to the resources they need to perform their tasks. This reduces the potential damage if an account is compromised.
Assume Breach means organizations should operate as if a breach has already occurred. This approach focuses on minimizing impact and detecting threats quickly.
Key Components of Zero Trust Architecture
The Zero Trust model relies on multiple components working together to secure cloud environments.
Identity and Access Management (IAM)
IAM systems verify user identities and control access to resources. Strong authentication methods like multi-factor authentication are essential in this model.
Device Security
Every device accessing the cloud must meet security standards. Devices are checked for compliance, updates, and potential vulnerabilities before granting access.
Network Segmentation
Zero Trust divides networks into smaller segments, limiting access between them. This prevents attackers from moving freely within the system.
Continuous Monitoring
Security systems continuously monitor user behavior and network activity to detect anomalies and potential threats in real time.
Data Protection
Sensitive data is protected using encryption and strict access controls, ensuring it remains secure even if accessed by unauthorized users.
How Zero Trust Works in the Cloud
In a cloud environment, Zero Trust operates by evaluating every access request based on multiple factors such as user identity, device health, location, and behavior.
For example, even if a user logs in with correct credentials, additional checks like device compliance or unusual login activity may trigger further verification.
Access is granted only when all security conditions are satisfied, and it can be revoked instantly if any risk is detected.
Benefits of the Zero Trust Security Model
Zero Trust offers several advantages for businesses using cloud computing.
It significantly reduces the risk of data breaches by eliminating implicit trust. It improves visibility into user activity and enhances control over access.
The model also supports remote work by securely enabling access from any location. Additionally, it helps organizations meet compliance requirements by enforcing strict security policies.
Challenges of Implementing Zero Trust
Despite its benefits, implementing Zero Trust can be complex.
Organizations may face challenges in integrating existing systems, managing identities across platforms, and ensuring user convenience while maintaining security.
It also requires continuous monitoring and advanced tools, which can increase operational complexity.
However, these challenges can be managed with proper planning and phased implementation.
Best Practices for Zero Trust Implementation
To successfully implement Zero Trust, organizations should start by identifying critical assets and sensitive data.
Strong IAM policies should be established with multi-factor authentication and least-privilege access. Network segmentation should be applied to limit lateral movement.
Continuous monitoring and automated threat detection tools should be used to identify risks in real time.
Regular audits and employee training are also important to ensure that security practices are followed consistently.
Future of Zero Trust in Cloud Security
Zero Trust is becoming a standard approach in modern cybersecurity.
With the integration of artificial intelligence and machine learning, Zero Trust systems are becoming more intelligent and capable of detecting threats faster.
As cloud adoption continues to grow, Zero Trust will play a crucial role in securing digital environments and protecting against evolving cyber threats.