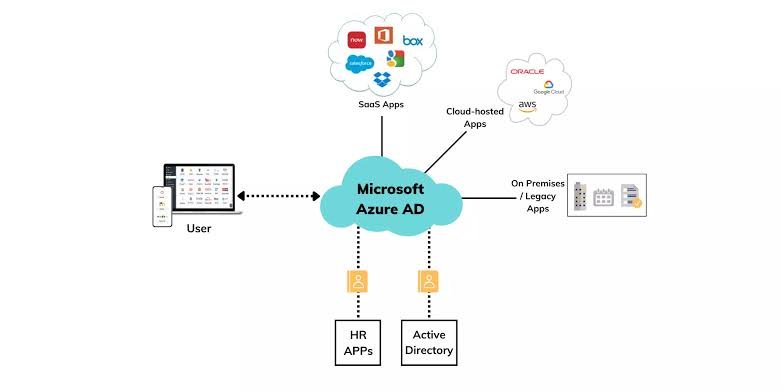
Azure Active Directory (Azure AD), now evolving toward Microsoft Entra ID, is Microsoft's cloud-native identity and access management (IAM) service that centralizes authentication for users, apps, and devices across cloud, on-premises, and hybrid setups. It replaces traditional on-prem Active Directory for modern workloads, handling billions of logins daily with 99.99% uptime across global data centers.
Unlike legacy AD, Azure AD focuses on cloud identities, supporting OAuth, OpenID Connect, and SAML for SSO to thousands of SaaS apps like Office 365, Salesforce, and custom APIs. Developers integrate it via SDKs in .NET, Java, or Node.js for token-based auth.
For cloud security analysts in India managing SEO platforms or digital marketing tools, Azure AD ensures compliant access to Azure resources like VMs and AKS clusters discussed earlier.
Core Features of Azure Active Directory
Azure AD's Single Sign-On (SSO) lets users access multiple apps with one login, slashing password fatigue and boosting productivity by 30-50% in enterprises. Multi-Factor Authentication (MFA) adds biometrics, SMS, or app push for 99.9% phishing resistance.
Conditional Access policies evaluate risk signals like location, device compliance, or IP reputation before granting entry to block logins from risky nations dynamically. Identity Protection uses ML to detect leaked credentials or impossible travel, auto-remediating 85% of threats.
Self-Service Password Reset (SSPR) and privileged identity management (PIM) minimize admin intervention; Application Proxy publishes on-prem apps securely without VPNs.
Editions and Pricing Tiers
Free edition covers basic directory services for up to 500,000 objects. Premium P1 adds dynamic groups, MFA, and hybrid sync ($6/user/month); P2 includes Identity Protection and entitlement management ($9/user/month). B2B/B2C for external guests scales to millions.
Developers start free, upgrading for advanced RBAC in DevOps pipelines, integrating with GitHub or Azure DevOps.
How Azure AD Works Under the Hood
Users authenticate via password hash sync, pass-thru auth, or federation with on-prem AD using Azure AD Connect. Tokens (JWT) issued post-validation carry claims for apps to authorize via scopes.
Directory replication across primary/passive partitions ensures HA; Entra ID governance automates lifecycle, like access reviews. API-driven management via Microsoft Graph lets scripts query users: GET https://graph.microsoft.com/v1.0/users.
Benefits for Developers and Businesses
Azure AD cuts IT costs by 40% through automation, reducing helpdesk tickets via SSPR and delegated admin. High availability (99.9% SLA) spans 28+ regions, ideal for global teams in Gurugram handling UAE e-commerce logins.
Security posture improves with zero-trust principles: verify explicitly, assume breach. Productivity surges as users switch apps seamlessly; integration with Intune enforces device compliance for BYOD.
For digital marketers, secure API access to analytics tools prevents data leaks during campaign scaling.
Setting Up Azure AD: Developer Quickstart
Create a tenant at portal.azure.com > Azure Active Directory > Create tenant. Add users/groups, enable SSO for apps via the Enterprise Applications blade.
Sync on-prem: Install Azure AD Connect, select hybrid join. Code sample: Register app, get client ID/secret, acquire token:
text
POST https://login.microsoftonline.com/{tenant}/oauth2/v2.0/token
Test with Postman for AKS or VM auth as in prior guides.
Enable MFA globally or per-user; set conditional policy: if risky-signin = high, block.
Integrating with Azure Services
Azure AD secures AKS via RBAC, binds Entra groups to Kubernetes roles. Gate VM RDP/SSH with JIT access pairs with Sentinel for SIEM, detecting anomalies across your estate.
For SEO/content apps, OAuth protects WordPress APIs; B2B invites contractors without licenses.
Advanced Security and Compliance
Privileged Identity Management (PIM) requires approval for elevation, audited via logs. Access Reviews automate certification; GDPR/HIPAA compliance via data residency controls.
Block legacy auth protocols; integrate with Defender for Identity to hunt on-prem threats. Developers use the Microsoft Graph API for custom risk policies.
Hybrid Identity Scenarios
Azure AD Connect syncs 90% of enterprises' on-prem AD, enabling password hash auth or federation. Seamless SSO for domain-joined devices uses Kerberos tickets.
Migrate gradually: Pilot cloud-only users, then hybrid join Azure VMs for unified management.
Cost Management and Optimization
Free tier suffices for devs; scale P1/P2 per active user. Monitor via Azure AD reports > Sign-in logs; unused licenses auto-deprovision via governance.
Avoid over-provisioning groups; use dynamic membership queries for efficiency.
Monitoring and Troubleshooting
Audit logs track changes; Sign-in reports flag failures (e.g., invalid grants). Common fixes: Reset service principal secrets, check app permissions in Manifest.
Integrate with Application Insights for app-level traces; alerts on brute-force via Identity Protection.
Real-World Use Cases
Digital agencies use Azure AD for secure client portals, SSO to Google Ads/GA4. E-commerce flowers biz in UAE authenticates mobile apps. Cloud security audits leverage PIM for least-privilege.
DevOps: Entra ID OIDC provider for GitHub Actions, deploying to AKS/VMs from earlier blogs.
Future of Azure Active Directory
Microsoft Entra ID expands passwordless (FIDO2), verifiable credentials, and AI-driven protection, with deeper integration with Copilot for natural language policy creation.
Cloud pros, layer Azure AD atop VMs/AKS for zero-trust; start prototyping today for resilient identities.