Cloud security audits systematically evaluate your cloud infrastructure, configurations, access controls, and compliance to identify risks before breaches occur. In dynamic environments like multi-cloud setups, regular audits prevent misconfigurations that cause 80% of incidents. They align with frameworks such as NIST, CSA CCM, and provider-specific guidelines from AWS or Azure.
For DevOps teams, audits shift security left, integrating into CI/CD for continuous validation. This process not only meets regulatory demands like GDPR or SOC 2 but also builds resilience against evolving threats like supply chain attacks.
Why Conduct Regular Cloud Security Audits
Traditional perimeter security fails in cloud-native apps with ephemeral workloads and serverless functions, making audits essential for visibility into shadow IT and over-privileged accounts. Audits reduce mean time to detect threats and provide actionable insights for remediation. Organizations performing quarterly audits report 40% fewer compliance violations.
They also support Zero Trust principles by verifying every access and workload, tying directly into monitoring tools like those discussed previously for DevOps. In 2026, with rising ransomware targeting clouds, audits are non-negotiable for business continuity.
Preparation Before the Audit
Begin by defining clear objectives based on your risk profile, compliance needs, and business priorities, such as focusing on high-value data stores or Kubernetes clusters. Assemble a cross-functional team including security, DevOps, and cloud architects, and select tools like CSPM platforms for automated scanning.
Review contracts with cloud providers to understand shared responsibility models, ensure SOC reports and penetration test results are available. Set timelines, typically 2-4 weeks, and establish baselines using historical logs from CloudTrail or equivalent.
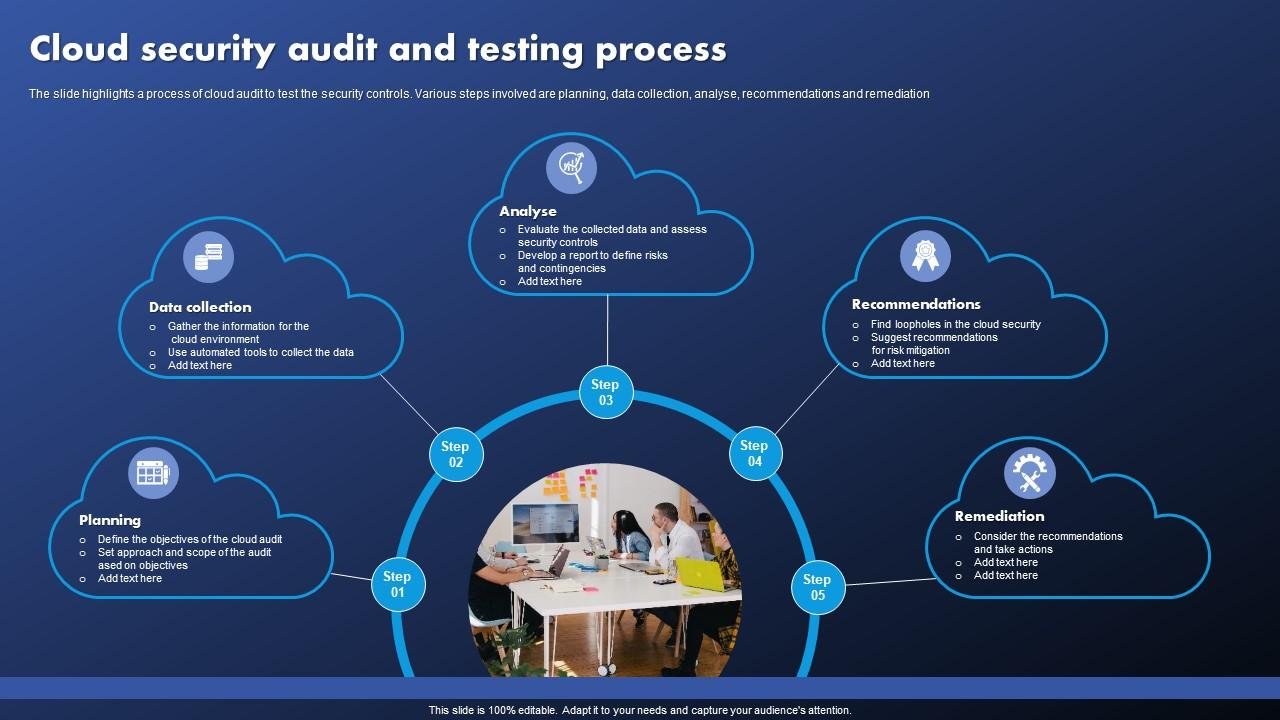
Step-by-Step Guide to Performing the Audit
Step 1: Define Scope and Goals
Narrow the audit to specific accounts, regions, services, or workloads to avoid overload. Prioritize crown jewel assets like databases and APIs. Align goals with standards like ISO 27001 or PCI DSS, documenting assumptions and exclusions for transparency.
Engage stakeholders early to map dependencies, ensuring the scope covers identities, networks, data flows, and third-party integrations. This step prevents scope creep and focuses efforts on the highest-impact areas.
Step 2: Evaluate Cloud Provider Security Posture
Assess your provider's controls, including encryption at rest/transit, DDoS protection, and compliance certifications via their trust portals. Request audit logs and review SLAs for incident response times. Verify features like AWS GuardDuty or Azure Defender are enabled.
Compare against your requirements if using multi-cloud, standardize checklists across providers to identify variances in security baselines.
Step 3: Inventory Assets and Map Attack Surface
Use native tools like AWS Resource Explorer or Azure Resource Graph to discover all resources, including unmanaged ones like forgotten S3 buckets. Classify data by sensitivity and tag assets for risk scoring.
Map lateral movement paths, identifying public exposures, unused permissions, and supply chain risks from Lambda functions or containers—Automate with agents or agentless scanners for comprehensive coverage.
Step 4: Review Access Controls and Identity Management
Audit IAM policies for least privilege, can for admin over-provisions using tools like IAM Access Analyzer. Verify MFA enforcement, just-in-time access, and service account rotations. Check for dormant users and external identity federation.
Examine RBAC in Kubernetes or VPC peering for excessive trusts, ensuring contextual policies block anomalous logins based on location or device posture.
Step 5: Assess Configurations, Vulnerabilities, and Network Security
Scan for misconfigurations like open ports or unencrypted storage using CSPM or Nessus. Run vulnerability assessments on images, VMs, and apps, prioritizing CVEs by exploitability. Test network segmentation with tools simulating east-west attacks.
Review logging and monitoring to ensure retention meets compliance, with alerts for failed authentications or API anomalies. Simulate breaches via purple team exercises.
Step 6: Check Compliance and Document Findings
Cross-reference against frameworks, generating reports on gaps like missing WAF rules or unpatched OS. Quantify risks with CVSS scores and business impact analysis.
Compile a detailed report with executive summaries, technical findings, evidence screenshots, and prioritized recommendations. Share via secure portals for stakeholder review.
Step 7: Develop Remediation Plan and Verify Fixes
Prioritize fixes by risk tier, immediate for criticals like public buckets. Assign owners, timelines, and metrics like closure rates—re-audit post-remediation to confirm efficacy.
Integrate findings into DevOps pipelines for automated checks, fostering a culture of continuous auditing.
Tools to Streamline the Process
Leverage cloud-native options like AWS Audit Manager, Azure Policy, or Google Security Command Center alongside third-party CNAPPs such as Wiz, Prisma Cloud, or Orca Security. These integrate with Slack and Jira for DevOps-friendly workflows, providing dashboards for real-time posture.
Open-source alternatives like Prowler or Scout Suite offer cost-effective starting points for SMBs.
Common Challenges and Best Practices
Overcome visibility gaps by combining agent-based and agentless scanning, and address false positives through baselining. For large environments, adopt risk-based auditing over exhaustive checks. Train teams on cloud-specific threats to improve adoption.
Schedule audits quarterly, automating 80% via IaC scanning in pipelines. Pair with penetration testing for validation.
Measuring Audit Success and Next Steps
Track KPIs like risk score reduction, audit cycle time, and coverage percentage. Use maturity models from CSA to benchmark progress. Evolve to continuous controls monitoring for proactive security in fast-scaling clouds.