Cloud environments power modern enterprises, but they also attract sophisticated attackers targeting misconfigurations and weak controls, leading to costly data breaches. With incidents like exposed databases and API vulnerabilities on the rise, prevention hinges on a defense-in-depth model that layers preventive, detective, and responsive controls across identity, data, networks, and people.
Breaches often stem from human error or overlooked gaps in the shared responsibility model. Providers secure the infrastructure, but organizations must lock down their usage. Adopting zero-trust architecture shifts from perimeter defense to continuous verification, drastically reducing unauthorized access risks in dynamic multi-cloud setups.
Strengthen Identity and Access Management
Weak credentials cause most breaches; lock them down first. Enforce multi-factor authentication (MFA) everywhere, prioritizing phishing-resistant options like hardware tokens over SMS. Implement the principle of least privilege using role-based access control (RBAC), granting minimal permissions and auditing them quarterly to revoke excesses.
Just-in-time (JIT) privileges for admins eliminate standing risks, auto-expiring after use. Centralized IAM federated across AWS IAM, Azure AD, and Google Cloud IAM prevents sprawl, while tools scan for dormant accounts that attackers hijack. This foundation stops 80% of initial access vectors.
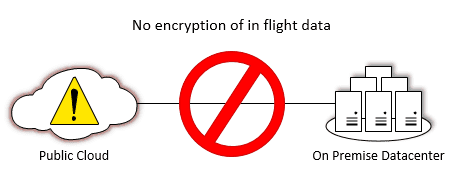
Encrypt and Tokenize Sensitive Data
Unencrypted data is low-hanging fruit for thieves. Apply end-to-end encryption: customer-managed keys for data at rest via KMS services, TLS 1.3 for transit, and confidential computing for processing. Rotate keys automatically and classify data to prioritize crown jewels like customer PII.
Tokenization replaces sensitive values in dev/test environments, minimizing exposure. Data masking ensures compliance during analytics, while immutable storage thwarts ransomware encryption. These measures render stolen data worthless, even if exfiltrated.
Secure Network Architectures
Lateral movement amplifies breaches ruthlessly. Deploy micro-segmentation with workload-level policies, using security groups and network ACLs to block east-west traffic. Cloud-native firewalls like AWS Network Firewall enforce consistent rules across hybrid setups.
Private endpoints for services hide them from the public internet, and VPC peering with encryption prevents leaks. Intrusion prevention systems (IPS) inspect flows in real-time, flagging anomalies like port scans. This containment limits the blast radius dramatically.
Deploy Data Loss Prevention and Monitoring
Blind spots breed breaches; gain visibility. Cloud Security Posture Management (CSPM) scans configurations continuously for public buckets or lax APIs. Data Loss Prevention (DLP) tools monitor exfiltration patterns, SSNs in uploads or bulk downloads, and quarantine suspicious activity.
Centralize logs in SIEM with UEBA for behavioral baselines, alerting on deviations like logins from unusual geos. AI-driven threat hunting prioritizes signals, integrating SOAR for automated responses like instance isolation. Daily reviews catch what automation misses.
Automate Security in DevOps Pipelines
Manual configs invite driftshift left. Infrastructure as Code (IaC) with policy-as-code (OPA) rejects insecure deployments at CI/CD gate. Container scanning in registries blocks vulnerable images, and serverless functions get runtime protections.
Immutable infrastructure prevents tampering, with blue-green deployments for safe rollouts. Compliance automation aligns with NIST and CIS, ensuring audits pass effortlessly. This embeds security without slowing innovation.
Manage Third-Party and Supply Chain Risks
Vendors introduce hidden doors rigorously. Demand SOC 2 reports and right-to-audit clauses, monitoring SaaS via CASB for shadow IT. Scan dependencies in pipelines to block SolarWinds-style compromises.
Contractual SLAs define breach notification timelines, with regular penetration tests validating joint controls. Endpoint detection on user devices stops local pivots to cloud resources.
Build Incident Response and Culture
Preparation averts disaster. Develop playbooks for breach scenarios, tested via tabletop exercises quarterly. Train teams on phishing, secure coding, and reporting. Human error fuels most incidents.
Metrics like MTTD/MTTR drive maturity, with security champions per team fostering accountability. Backup strategies with air-gapped immutability ensure recovery without ransom payment.
Preventing data breaches in cloud environments demands vigilance and iteration, starting with IAM and encryption, layer monitoring and automation and then culture. This holistic approach turns the cloud into a fortress, safeguarding assets while fueling growth.