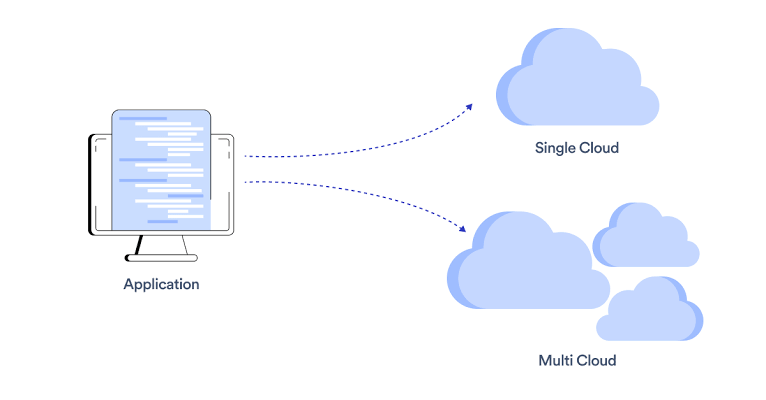
Enterprises increasingly adopt multi-cloud strategies to avoid vendor lock-in, optimize costs, and leverage specialized services across AWS, Azure, and Google Cloud. However, this complexity multiplies security risks like configuration drift, inconsistent policies, and expanded attack surfaces, making unified defense essential. A robust approach combines centralized management, zero-trust principles, and automation to maintain visibility and control without stifling agility.
The shared responsibility model varies by provider, demanding a tailored yet standardized strategy. Start by inventorying all resources, then layer identity federation, encryption standards, and continuous monitoring to bridge silos and prevent breaches that exploit gaps between clouds.
Establish Centralized Identity and Access Management
Fragmented identities breed vulnerabilities; unify them first. Deploy single sign-on (SSO) with protocols like SAML or OIDC across providers, using tools such as Okta or Azure AD for federated IAM that enforces consistent multi-factor authentication (MFA) and role-based access control (RBAC).
The principle of least privilege applies universally: map roles to cross-cloud permissions and use just-in-time (JIT) elevation for admins. Automated audits detect over-privileged service accounts or orphans, while zero-trust verifies every access request by context, user, device, eliminating implicit trust between clouds.
Standardize Encryption and Key Management
Data must remain protected regardless of the provider. Mandate end-to-end encryption with customer-managed keys (CMKs) via Bring Your Own Key (BYOK) models, centralizing rotation and access through services like HashiCorp Vault or AWS KMS with cross-cloud replication.
Enforce TLS 1.3 for transit and confidential computing for in-use processing, ensuring uniformity via policy engines. Data classification tags trigger provider-agnostic protections, like tokenization for dev environments, thwarting exfiltration even in hybrid flows.
Implement Network Segmentation and Connectivity
Multi-cloud sprawl invites lateral movement; compartmentalize aggressively. Use virtual private clouds (VPCs) with micro-segmentation policies applied consistently via tools like Avi Networks or native security groups, blocking unauthorized east-west traffic.
Secure interconnects with encrypted peering (e.g., AWS Transit Gateway to Azure ExpressRoute) and third-party fabrics like Megaport for low-latency, zero-trust links. Cloud-native firewalls and intrusion detection systems (IDS) inspect all flows, with allow-lists over deny-lists for precision.
Deploy Unified Security Posture Management
Blind spots across providers are fatal to gaining holistic visibility. Cloud Security Posture Management (CSPM) platforms like Prisma Cloud or Orca Security scan configurations in real-time for misconfigurations, such as public endpoints or lax APIs, normalizing risks into a single dashboard.
Integrate Cloud Workload Protection Platforms (CWPP) for runtime threats, using AI to correlate anomalies across environments. SIEM aggregation from CloudTrail, Azure Monitor, and GCP Audit Logs enables unified threat hunting and alerting.
Automate Governance and Compliance
Manual oversight fails at scale. Code your policies. Infrastructure as Code (IaC) with policy-as-code (e.g., Open Policy Agent) enforces standards in CI/CD pipelines, rejecting drifts before deployment across Terraform or Pulumi configs.
Vendor-neutral frameworks like NIST or CIS Benchmarks guide tagging for ownership, residency, and sensitivity. Automated compliance reporting streamlines audits, with drift detection triggering self-healing workflows.
Secure Workloads and Supply Chain
Containers and serverless span clouds protect them uniformly. Scan images in multi-registry setups with tools like Aqua or Sysdig, applying runtime policies via eBPF for Kubernetes consistency. Shift-left testing in pipelines catches vulnerabilities early.
Vet third parties with standardized SLAs and CASB oversight for SaaS sprawl. Immutable infrastructure and blue-green deployments minimize runtime risks.
Foster Multi-Cloud Incident Response and Culture
Coordination prevents chaos during breaches. Unified playbooks tested via cross-cloud simulations ensure rapid isolation, with shared logging accelerating forensics. Train teams on provider-specific nuances while emphasizing universal best practices like phishing awareness.
Metrics tracking mean time to detect/remediate (MTTD/MTTR) drive maturity, with security operations centers (SOCs) leveraging MSSPs for 24/7 coverage.
Securing a multi-cloud architecture transforms complexity into strength through standardization and automation. Prioritize IAM and visibility first, then scale layers for resilient, compliant operations that support enterprise innovation.