As cloud adoption continues to accelerate, the threat landscape is evolving just as rapidly. In 2026, cybercriminals are leveraging advanced technologies like artificial intelligence, exploiting complex cloud environments, and targeting new attack surfaces.
Understanding these threats is essential for businesses to protect their cloud infrastructure, data, and applications effectively.
The Evolving Cloud Threat Landscape
Modern cloud environments are no longer simple systems—they involve multi-cloud setups, APIs, containers, and AI-driven services. This complexity has significantly increased the attack surface.
Recent reports show a sharp rise in cloud-related incidents, with a 154% increase in attacks in 2026, largely due to misconfigurations and unpatched systems. Attackers are also shifting their focus from traditional endpoints to cloud ecosystems and software supply chains.
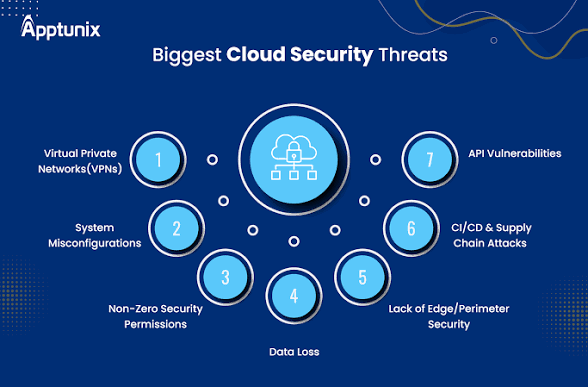
Top Cloud Security Threats in 2026
Data Breaches and Unauthorized Access
Data breaches remain one of the most critical threats in cloud environments. They occur when attackers gain access to sensitive data due to weak authentication, poor encryption, or misconfigured storage.
Human error plays a major role, with many breaches caused by incorrectly configured cloud services or exposed databases.
Misconfigurations of Cloud Resources
Misconfigured storage buckets, databases, and access controls are among the most common vulnerabilities. Even a small mistake in configuration can expose entire systems to the public internet.
Studies show that a significant percentage of cloud security incidents are directly linked to misconfigurations and poor setup practices.
Identity and Access Management (IAM) Weaknesses
In 2026, identity has become the new security perimeter. Weak IAM policies, excessive permissions, and credential theft can allow attackers to move laterally within cloud environments.
Token theft and session hijacking are increasingly used to gain unauthorized access to cloud systems.
Insecure APIs and Interfaces
Cloud services rely heavily on APIs for communication. If these APIs are not properly secured, they can become entry points for attackers.
API abuse, including unauthorized requests and data manipulation, is one of the fastest-growing cloud security risks.
AI-Powered and Automated Attacks
Artificial intelligence is now being used by cybercriminals to automate attacks, making them faster and more sophisticated. Reports indicate an 89% increase in AI-enabled cyberattacks, highlighting how attackers are scaling their operations.
AI is also being used for phishing, vulnerability discovery, and bypassing traditional security systems.
Third-Party and Supply Chain Vulnerabilities
Attackers are increasingly targeting third-party integrations, software dependencies, and supply chains instead of directly attacking cloud infrastructure.
Recent findings show that 44.5% of cloud intrusions originate from third-party vulnerabilities, making them a major concern in 2026 .
Insider Threats and Human Error
Employees, contractors, or partners with access to cloud systems can unintentionally or intentionally cause security incidents.
Lack of training, misuse of credentials, or negligence often leads to data leaks and unauthorized access.
Zero-Day Vulnerabilities and Unpatched Systems
Zero-day vulnerabilities—flaws that are exploited before patches are available—are increasing significantly. There has been a 42% rise in zero-day exploit activity, making timely patching more critical than ever.
Unpatched systems remain a major entry point for attackers.
Cloud-Native Malware and Ransomware
Cloud environments are now targeted by specialized malware designed to exploit containers, serverless functions, and cloud workloads.
Ransomware attacks can encrypt cloud data and disrupt operations, forcing businesses to pay large sums to regain access.
Lack of Visibility and Monitoring
Modern cloud environments are dynamic, with resources constantly being created and destroyed. This makes it difficult for traditional security tools to maintain visibility.
Limited monitoring can allow attackers to remain undetected for long periods, increasing the damage caused.
Emerging Threat: Quantum Computing Risks
A new and future-facing threat is quantum computing, which has the potential to break traditional encryption methods. Experts warn that powerful quantum systems could compromise current cryptographic standards in the coming years.
Organizations are now being encouraged to prepare for post-quantum security.
Key Vulnerabilities in Cloud Environments
Beyond threats, vulnerabilities are weaknesses that attackers exploit. In 2026, the most critical vulnerabilities include:
- Poor configuration management leading to exposed resources
- Weak authentication systems and a lack of multi-factor authentication
- Unsecured APIs and endpoints
- Outdated software and dependencies
- Insufficient encryption practices
- Lack of real-time monitoring and logging
These vulnerabilities often arise from complexity, lack of expertise, and rapid cloud adoption.
Why These Threats Are Increasing
Several factors are contributing to the rise in cloud security risks.
The rapid adoption of multi-cloud and hybrid environments has increased complexity. AI and automation are making attacks faster and more scalable. Organizations are also struggling with a shortage of skilled cybersecurity professionals, creating gaps in defense systems .
Additionally, the growing reliance on third-party services and open-source components has expanded the attack surface.
How Businesses Can Mitigate These Risks
To combat modern cloud threats, businesses must adopt a proactive security approach.
Implementing a Zero Trust model ensures that no user or system is trusted by default. Strong IAM policies, including least-privilege access and multi-factor authentication, are essential.
Regular security audits, automated monitoring, and real-time threat detection can help identify risks early. Organizations should also keep systems updated and patch vulnerabilities promptly.
Securing APIs, encrypting sensitive data, and training employees on security best practices are equally important.